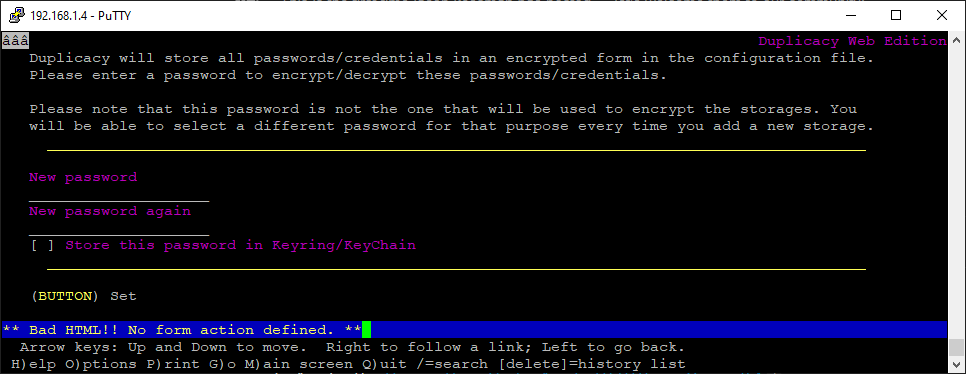
No, web-gui shall be already running, otherwise your backups won’t run. You would need to setup systemd service to start duplicacy-web when the server starts.
The ssh in this thread is only to create a tunnel to your server. If you only do that in the trusted lan then it’s indeed overkill, and you can configure duplicacy to listen to all interfaces (0.0.0.0) per comment above (or directly in the settings.json file) and then connect from anywhere.
There is another, my preferred solution, is to use cloudflare zero trust, thus allowing to connect to duplicacy webui (or to any other private web service in your lan) from anywhere in the world, without messing with vpns, tunnels, ports, or firewalls, protected by cloudflare and identity provider of your choice.
That said, there are of course ways to start an app via ssh session in a way that will let it survive session disconnect, if that is what you want to do.
One way is to start tmux session and launch app there. When ssh disconnects — app will continue running in the tmux session.
Another — use disown command of your shell. For example,
% ssh me@myserver
# /usr/local/bin/my_app & disown
# exit
%
Have a look at the first comment to this blog post: Duplicacy Web on Synology Diskstation without Docker | Trinkets, Odds, and Ends. The example service definition file is there provided by the fellow kind user.