Hi,
I’ve been testing out Duplicacy CLI on Ubuntu 18.04, and am quite pleased with it. One thing I haven’t been able to figure out, though, is how to store the storage/encryption password in an encrypted form somewhere.
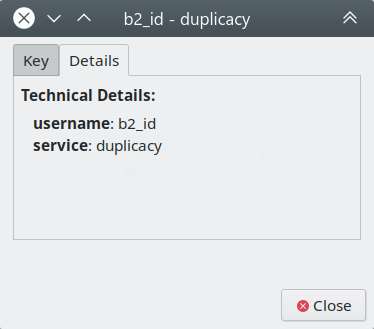
According to the guide (Passwords, credentials and environment variables), once I enter the password for the first time it should be stored in the keyring, but that doesn’t seem to happen: I either have to enter it each time, or add it to the preferences file (plain-text).
Testing with the Web GUI the password does get stored, so the mechanism itself seems to work.
Anyone have any ideas what the problem might be, or how to troubleshoot the issue?
Thanks!
P.S. Not sure if it makes any difference, but I’m using the KDE desktop - nothing related to Duplicacy is stored in the KDE wallet, nor are there any DUPLICACY_ environment variables.

 button on the posts that you found useful.
button on the posts that you found useful. box under the post. That of course may include your own post
box under the post. That of course may include your own post