According to the v1 web edition release notes, this was recently added.
Basically, use the Password field for the passphrase protecting the key file (otherwise, that Password field is for the sftp password when not using a key file - hence it doubles up as the passphrase, as the two are mutually exclusive).
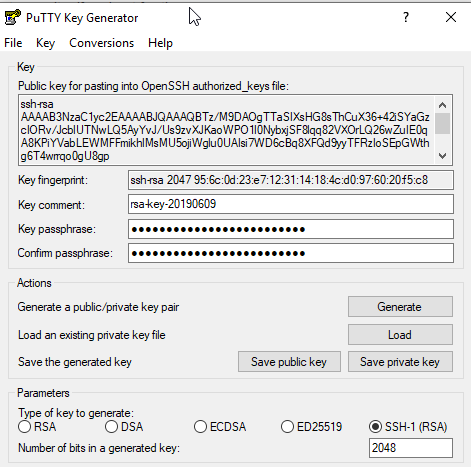
As for parameters, I’d personally stick with RSA 2048 (left-most radio button).
SSH-1 (RSA) is very weak and should be considered broken. DSA is even weaker and definitely broken. 
ECDSA and ED25519 are new - I believe the latter is the strongest and has other benefits - so long as your SSH server supports it, you may have to tinker with the /etc/sshd_config on the server to get it working. RSA 2048 should just work, and is pretty secure.