Download links:
https://acrosync.com/duplicacy-web/duplicacy_web_installer_win64_1.5.0.exe
https://acrosync.com/duplicacy-web/duplicacy_web_osx_x64_1.5.0.dmg
https://acrosync.com/duplicacy-web/duplicacy_web_freebsd_x64_1.5.0
https://acrosync.com/duplicacy-web/duplicacy_web_linux_x64_1.5.0
https://acrosync.com/duplicacy-web/duplicacy_web_linux_i386_1.5.0
https://acrosync.com/duplicacy-web/duplicacy_web_linux_arm64_1.5.0
https://acrosync.com/duplicacy-web/duplicacy_web_linux_arm_1.5.0
https://acrosync.com/duplicacy-web/duplicacy_web_linux_armv7_1.5.0
Changes:
- Add options for RSA encryption and Erasure Coding when configuring a new storage
- Accept custom HTTPS certificates placed under
~/.duplicacy-web/certs[1] - Fixed a bug in the include/exclude pattern set up dialog that caused some characters to be wrongly url-encoded
- Fixed a bug where a deleted schedule causes other running schedules to never finish
- Fixed the progress bar for check and copy jobs
- Fixed mismatched graph colors
- Don’t add
-ato a check job if a backup id is already specified with the-idoption - Add a date field when sending emails
- Show the expiration date of lifetime licenses correctly (which never expire)
- On FreeBSD fail over to our own keyring implementation if the default one is not available
- Automatically skip files with the extended attribute
com.apple.metadata:com_apple_backup_excludeItemfor new backups on macOS [2] - Prompt for enabling Full Disk Access if not enabled on macOS
- Set the number of threads to 4 for most cloud storages when adding a new backup job
- Make the log viewer most responsive
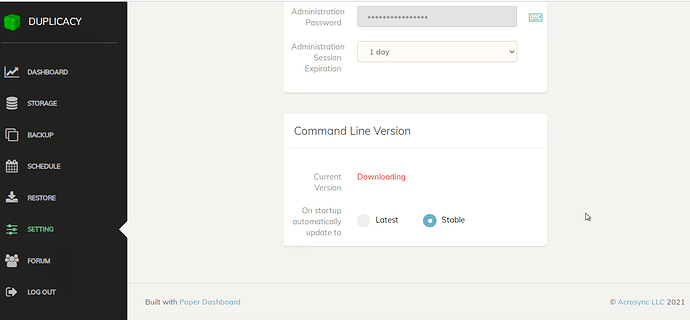
- Use https://duplicacy.com/latest_cli_version to find the latest/stable CLI version
- Show the remote ip address in the log when an incorrect administration password is entered
Notes:
[1] You’ll need to create 2 files under ~/.duplicacy-web/certs: domain.crt contains the full chain certificates and domain.key is the private key (domain should be replaced by the actual domain name).
[2] This is done by setting the preference key exclude_by_attribute to true in new backups created in 1.5.0, which means existing backups will not skip these files by default. If you want to change this behavior for existing backups, manually modify the preference key exclude_by_attribute in ~/.duplicacy-web/duplicacy.json to true.